Security vs Performance Tradeoffs in Modern Applications

Modern enterprise applications must achieve both robust security and high performance. In distributed cloud native and microservices environments every security control from encryption protocols to authentication imposes measurable overhead. Understanding these tradeoffs is key to building scalable secure systems without creating bottlenecks.
Security and performance are not binary choices. They are design constraints that shape architecture developer workflows and infrastructure decisions. This article examines how to balance these forces with practical patterns that minimize latency while protecting systems against threats.
Security Considerations in Modern Applications
Ensuring robust security in modern applications is not optional. Every application layer from front end to backend APIs requires mechanisms that protect data, control access, and defend against malicious activity. These security controls are designed to maintain confidentiality, integrity, and availability which is also called the CIA triad in cybersecurity.
Modern applications operate in distributed environments including cloud native platforms and microservices architectures. This makes security considerations both complex and critical. Implementing the right controls ensures that sensitive information remains protected, users are authenticated correctly, and systems remain resilient under attack.
Security mechanisms can be grouped into three key categories Data Protection Identity and Access Management and Threat Protection. Understanding each layer helps engineers design applications that balance protection with performance.
Data Protection
Data is one of the most valuable assets in any application. Protecting it requires encryption both in transit and at rest.
- TLS and SSL for Data in Transit – Transport Layer Security and its predecessor SSL encrypt data transmitted over networks. This prevents eavesdropping or tampering when data moves between clients, servers, or third party APIs. Engineers must ensure TLS 1.2 or higher is used with modern cipher suites for maximum security.
- Encryption at Rest – Data stored on disks or within databases should be encrypted to prevent unauthorized access in case of breaches. Techniques include full disk encryption, column level encryption for sensitive fields, and tokenization of personally identifiable information PII.
Identity and Access Management
Authentication and authorization are critical to ensuring that only legitimate users or systems can access specific resources.
- OAuth2 and OpenID Connect – Industry standard protocols for secure authorization and identity federation. These allow applications to manage user sessions safely and support single sign on across multiple systems.
- JWT and Token Based Authentication – JSON Web Tokens allow stateless authentication reducing server load while providing secure user verification. Tokens carry claims that determine access levels without repeated database queries.
- Role Based Access Control RBAC – Access rights are assigned based on roles rather than individuals reducing the risk of overprivileged accounts. RBAC simplifies permission management and enforces the principle of least privilege.
Threat Protection
Even with strong data and access controls applications must actively detect and prevent attacks.
- Web Application Firewalls WAFs – WAFs analyze incoming traffic to block malicious requests including SQL injection, cross site scripting, and API abuse. They act as the first line of defense against external attacks.
- Runtime Application Self Protection RASP – RASP monitors application behavior in real time. It can detect anomalies and prevent attacks from executing while the application is running providing internal safeguards beyond perimeter defenses.
Performance Impact of Security Controls
While these mechanisms are critical for application security they are not free. Implementing encryption, token validation, and real time threat detection consumes CPU and memory resources. Engineers must consider how each layer affects latency and throughput especially in high traffic or transaction intensive applications.
By designing security with performance in mind teams can maintain robust protection without compromising responsiveness. Techniques include caching validated tokens, selective encryption of sensitive data only, and offloading cryptographic operations to dedicated hardware accelerators.
Performance Considerations in Modern Applications
Performance is a key factor in modern applications. Users expect fast responses and smooth interactions while systems handle increasing workloads. For engineering teams, maintaining high performance alongside security and functionality is critical. Understanding key metrics and common bottlenecks helps design systems that are both responsive and reliable.
Key Performance Metrics
Application performance is commonly measured through latency, throughput, and resource utilization:
- Latency: This is the time required to process and respond to a user request. Low latency is essential for real time applications, interactive web platforms, and mobile services.
- Throughput: Throughput indicates how many requests or transactions a system can handle per second. It is especially important for APIs and cloud native services with high concurrency.
- Resource Utilization: CPU, memory, and input/output usage determine how efficiently an application uses infrastructure. High utilization can degrade response times and lead to system instability.
By monitoring these metrics, teams can pinpoint areas that need optimization while maintaining reliable user experience.
Common Performance Bottlenecks
Several factors can slow down applications, particularly when security controls are applied:
- Cryptographic Operations: Encryption and decryption protect data but consume CPU resources. Heavy encryption in high traffic systems can noticeably increase response times.
- Deep Packet Inspection: Security systems that inspect network traffic in depth can introduce latency, especially when analyzing large volumes of requests.
- Synchronous Validations: Repeated checks such as token verification, database validations, or authentication steps can create delays in high concurrency environments.
Understanding these bottlenecks allows teams to make tradeoff decisions between security and speed.
Real World Impact
Benchmarks show that encryption operations can increase latency by up to fifteen percent in transactional systems without hardware acceleration. This demonstrates the importance of designing systems with both security and performance in mind.
Optimization Strategies
To maintain performance while implementing security:
- Caching: Store validated tokens or frequently requested data to reduce repeated computation and database calls.
- Hardware Acceleration: Use specialized processors or chips for encryption to reduce CPU load.
- Asynchronous Processing: Move non critical validations or monitoring tasks to background processes to avoid slowing request processing.
- Selective Security Application: Apply full encryption or validation only to sensitive data or high risk operations while keeping other transactions lighter.
These strategies help engineering teams deliver fast, scalable, and secure applications that meet business and user expectations.
Architectural Tradeoffs Between Security and Performance
Modern applications must balance robust security with high performance. Every technical layer in an application introduces tradeoffs. Strong security controls protect sensitive data and prevent attacks but often consume computational resources and can impact responsiveness. Understanding these tradeoffs allows engineering teams to design systems that are both secure and efficient.
Encryption Overhead
Encryption is essential for protecting data both at rest and in transit. Strong algorithms such as AES 256 offer high levels of security. However, they consume significant CPU resources during encryption and decryption operations. In environments without optimized hardware such as AES NI or other cryptographic accelerators, encryption can increase response times and reduce throughput. Engineers must carefully choose algorithms and consider hardware acceleration to maintain performance while ensuring data confidentiality.
Authentication Latency
Authentication is critical to verify that users or systems are legitimate. Heavy authentication models such as multi factor authentication provide stronger security but add processing time. Every login or token validation introduces latency that can affect overall user experience. To minimize impact, teams can implement session caching, token expiration strategies, or adaptive authentication that only triggers multi factor validation in higher risk scenarios. These approaches balance security needs with application responsiveness.
Inspections and Scanning
Security inspection such as firewall filtering or deep packet analysis protects against attacks but adds overhead. Firewalls analyze traffic for suspicious patterns and deep packet inspection examines packet content in detail. While these measures are necessary to maintain security, they can increase latency and reduce throughput, especially in high volume environments. Removing these controls would expose the system to significant risk, so engineers must optimize inspection placement and combine them with load balancing to reduce performance impact.
Balancing Security and Performance
Architectural tradeoffs require careful planning. Engineering teams should evaluate which operations are critical for security and which can be optimized or deferred. For example, encryption can be applied selectively to sensitive data, authentication can be adaptive, and inspection can be offloaded or parallelized. Continuous monitoring and benchmarking help identify bottlenecks and ensure that security controls do not degrade user experience or system scalability.
Strategies for Mitigating Tradeoffs
Balancing security and performance requires deliberate strategies at both the code and architecture levels. By applying the right techniques, engineering teams can maintain robust security without unnecessarily degrading system responsiveness.
Efficient Cryptographic Choices
Choosing the right cryptography is critical for performance:
- Symmetric Encryption for Bulk Data – Symmetric algorithms such as AES GCM are faster than asymmetric algorithms and suitable for encrypting large volumes of data. They offer strong protection while minimizing CPU overhead, making them ideal for transactional and high throughput applications.
- Hardware Crypto Accelerators – Offloading encryption and decryption tasks to dedicated hardware such as AES NI or Trusted Platform Modules significantly reduces CPU load. Hardware acceleration allows systems to maintain strong security without impacting latency or throughput.
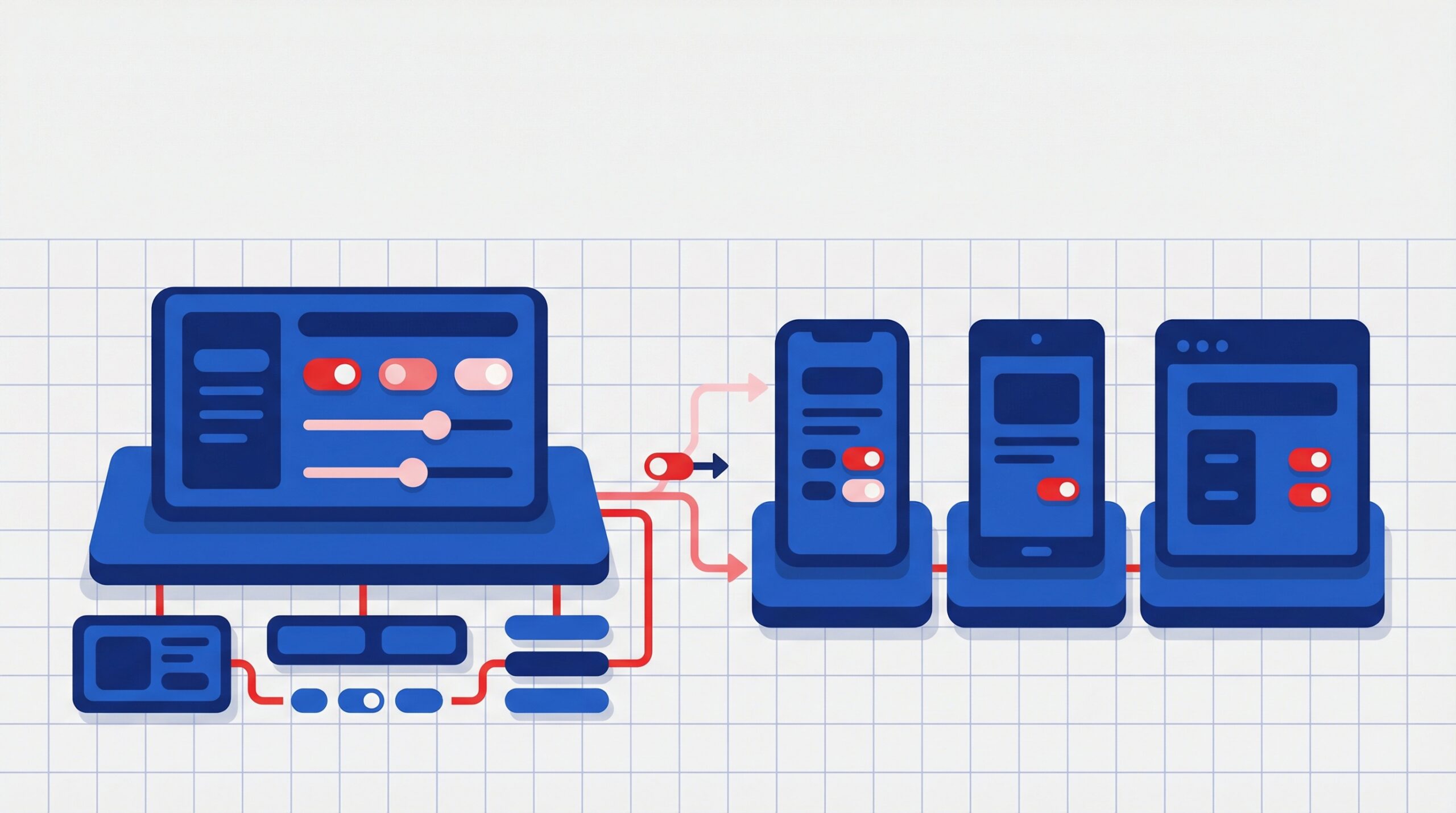
Architectural Techniques
Engineering teams can optimize system design to reduce performance impact:
- Asynchronous Security Checks – Moving non critical validations, logging, and monitoring to background processes reduces the load on primary request handling. This ensures that security operations do not block user interactions or slow transaction processing.
- Load Balancing and Caching – Caching frequently accessed static assets or validated tokens and distributing requests across multiple servers improves response times. These techniques allow security checks to remain effective while minimizing repeated computations for common requests.
Selective Security
Not all operations require the same level of scrutiny. Applying security rigor based on context improves efficiency:
- High Sensitivity Data – Transactions involving sensitive information or critical operations trigger full security checks including encryption, token validation, and real time monitoring.
- Non Critical Operations – Lower risk paths can bypass heavy security operations or use lighter checks, reducing computational overhead and improving overall application responsiveness.
By combining efficient cryptography, architectural optimizations, and context based security, teams can achieve a balance between strong protection and high performance. Continuous monitoring and adaptive strategies ensure that applications remain secure, scalable, and responsive under varying workloads.
Tools and Frameworks for Security and Performance
Modern applications require tools that help teams monitor performance, enforce security, and identify bottlenecks. Using the right combination of frameworks ensures both efficiency and protection.
| Category | Tools | Purpose |
|---|---|---|
| Performance Profiling | JMeter, Locust, Gatling | Evaluate application load capacity, measure latency, and identify performance bottlenecks |
| Security Analysis | OWASP ZAP, Burp Suite, Snyk | Detect vulnerabilities, perform automated security testing, and ensure application resilience |
| CI/CD Integration | GitHub Actions, GitLab CI | Integrate security and performance tests into deployment pipelines for early detection of issues |
| Monitoring | Grafana, New Relic | Collect telemetry for system performance, resource usage, and security events in real time |
These frameworks allow engineering teams to identify slow paths, detect security gaps, and optimize system architecture before they affect users. Combining profiling, security analysis, continuous integration, and monitoring creates a proactive approach to maintaining both security and performance.
Best Practices for Engineering Teams
Engineering teams face the ongoing challenge of balancing security and performance in modern applications. Following structured best practices ensures systems remain secure, responsive, and scalable.
Design with Intent
Planning is essential before implementing security or performance controls.
- Establish Performance Baselines – Measure latency, throughput, and resource utilization under normal workloads. Knowing baseline metrics helps teams evaluate the impact of new security layers and avoid unnecessary overhead.
- Incorporate Security and Performance in Architecture Reviews – Every architectural decision should consider both security and performance. From API design to data storage and service orchestration, reviewing tradeoffs early ensures better system efficiency and protection.
Observability
Visibility into how systems behave under real workloads allows teams to detect and address bottlenecks quickly.
- Distributed Tracing – Tools such as OpenTelemetry track how security checks and validations affect request flows. Engineers can identify slow paths and optimize operations without compromising protection.
- Instrumentation of Metrics – Monitor both security events and performance indicators continuously. Collecting metrics on CPU usage, memory, response times, encryption operations, and authentication workflows helps maintain a balance between safety and speed.
Iterative Refinement
Continuous measurement and incremental improvement are more effective than broad, simultaneous changes.
- Measure Impact Continuously – Track how each security or performance change affects latency, throughput, and user experience.
- Apply Incremental Adjustments – Simple adjustments such as caching validated sessions, optimizing encryption parameters, or adjusting request routing often yield significant performance gains while preserving security.
- Avoid Overly Broad Security Rollouts – Implementing all security controls at once can create bottlenecks. Gradual refinement allows teams to maintain responsiveness and scale efficiently.
By following these best practices, engineering teams can deliver applications that are secure, performant, and maintainable while reducing operational risks.
Future Trends
Security and performance will continue to evolve together as application architectures become more distributed and data intensive. Several emerging approaches are helping organizations strengthen protection while maintaining system efficiency.
- Zero Trust Architectures
Every request is authenticated and evaluated against access policies, improving security across modern cloud environments. - Confidential Computing
Hardware trusted execution environments protect sensitive data during processing with minimal performance overhead. - AI Assisted Profiling
Intelligent monitoring analyzes system behavior and dynamically adjusts security checks to reduce unnecessary processing.
As threats evolve, organizations must adopt architectures that protect systems without sacrificing responsiveness.
At Acmeminds, we help enterprises design secure, scalable, and high performance applications through modern architecture, performance optimization, and security focused engineering practices.
Conclusion
Security and performance must work together in modern applications. Strong protection is essential, but it should not slow down the systems users rely on every day.
By understanding where tradeoffs occur and applying the right architectural decisions, engineering teams can build systems that remain secure while delivering fast and reliable experiences.
Achieving this balance requires collaboration between security teams, developers, and product leaders so applications meet both performance expectations and risk requirements.
FAQs
1. What causes performance overhead in application security?
Security controls such as encryption, authentication checks, and deep inspection increase CPU usage and latency.
2. How much performance impact does encryption typically have?
Without acceleration, encryption can introduce measurable overhead—up to fifteen percent latency increase in real-world workloads.
3. Can we optimize security without degrading performance?
Yes, through selective encryption, hardware acceleration, and asynchronous checks.
4. What tools help measure security and performance tradeoffs?
Tools such as JMeter for performance and OWASP ZAP for security profiling help evaluate impacts.
5. Should security always be prioritized over performance?
Not always. Prioritize based on data sensitivity and risk profile. Critical assets may require stronger controls even at a performance cost.
6. What future technology helps reduce tradeoffs?
Zero trust architectures and confidential computing aim to reduce overhead while maintaining high security.
More on Apps

Web App LLM Integration Guide for Software Teams